With the Zoom Node Chat Hybrid module, customers can store chat data (currently, just chat message text) on-premises within their own storage infrastructure/datacenter instead of in the Zoom Cloud.
The Zoom Node Chat Hybrid module is intended to provide a solution for customers in highly regulated industries (such as FinServ), as well as customers operating within countries with regulations that require the data generated by their users to be stored within the geographical boundary of that country.
On-premise storage allows customers ownership of the chat data generated by their users, with the data residing in on-premise storage. While storage is on-premise, all Chat functionality will still reside in Zoom’s cloud. Specifically for the Chat Hybrid module, only the storage of chat data will be moved to the customer’s on-premise (databases) storage.
Depending on how on-prem storage is configured (Account or Group level) and who the user is chatting with (internal or external users), there are cases where a copy of a message may be stored in Zoom’s cloud as well as on-prem storage. For example, if the on-prem user is participating in a chat with a user who has Zoom cloud storage, a copy of the message is stored in Zoom’s cloud and in the on-prem location.
Chat Hybrid customers are expected to have in-house expertise for building out, deploying, and operating hardware and software infrastructure to support the storage needs of Zoom Chat platform. Zoom will provide guidelines regarding the required hardware and software. However, it is the responsibility of the customer to make the on-premise storage available to the Zoom cloud platform and provide database administration. Details on hardware and software requirements can be found here.
In addition, the following licensing needs to be purchased:
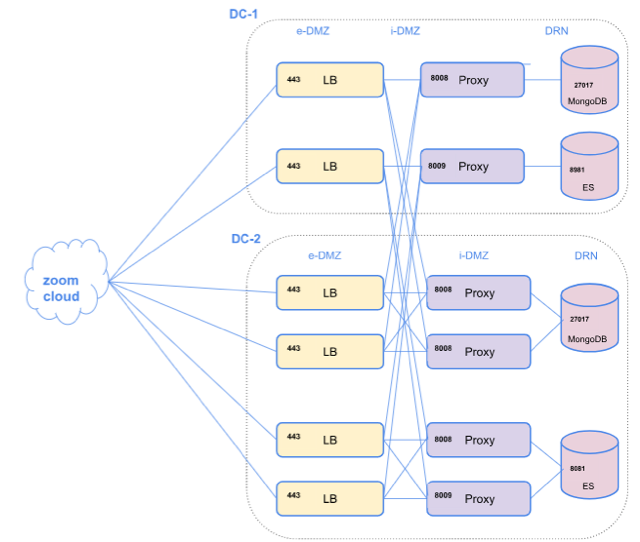
Below is a diagram of an example network schema for a deployed Chat Hybrid module and the associated database services that must also be deployed. The ports mentioned in the diagram and table below are not fixed and can be changed as required. All services mentioned below allow ports to be configured during the deployment.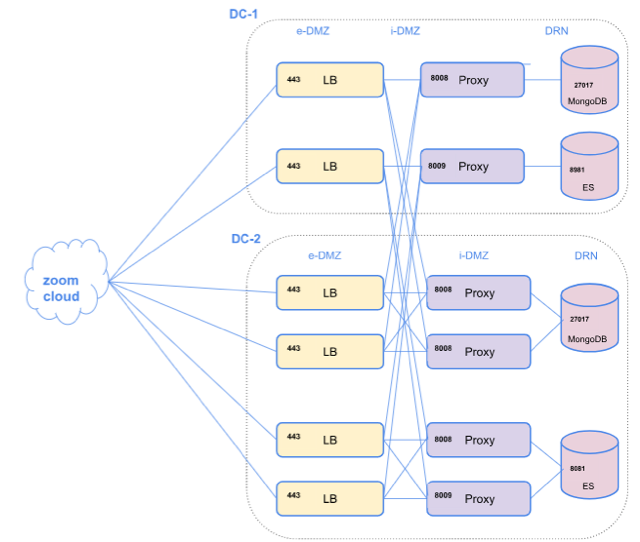
Below are the components and the communication ports utilized for the service:
| Service |
Caller | Port | Protocol |
| Load Balancer | Zoom Cloud Services (over internet) | 443 | HTTPS |
| MongoDB Proxy | Load Balancer (e-DMZ) | 8008 | HTTPS |
| ES Proxy | Load Balancer (e-DMZ) | 8009 | HTTPS |
| MongoDB | MongoDB Proxy (i-DMZ) | 27017 | TCP |
| Elastic Search | ES Proxy (i-DMZ) | 8081 | HTTPS |
Note: All servers in e-DMZ (i.e the load balancers) should have a public IP.